Mac security tips and tricks
Mac security is important, but often overlooked. It’s time to start taking the safety and security of your Mac seriously.
Maintaining privacy and keeping data secure are hugely important for any Mac user. Yet many of us give it scant attention and do little more than the bare minimum, if anything at all to ensure that hackers, opportunists and, yes, even the authorities are able to access as little of our personal data as possible.
Yet, macOS makes securing your data very simple, thanks to a host of tools in System Preferences and Safari, and several third party apps.
There are two places threats to your data are likely to come from: over a network like the internet, or from someone with direct access to your Mac. Taking steps to protect yourself will minimize both.
Mac security tips: The basics

Mac security tips: The basics
Let’s start with the basic Mac settings you should be checking to ensure security is watertight.
The first thing you should do is pay a visit to the Security & Privacy pane in System Preferences. Here, you’ll find four tabs that control various aspects of security.
To change settings you’ll need to click on the padlock at the bottom of the screen and type in your user name and password. If you have an administrator account, you’ll be able to make changes that affect the whole Mac, if not they’ll only apply to your account.
Mac security tips: Firewall

The first step to securing any Mac is enabling the firewall, which blocks any unwanted incoming network connections. You might think the firewall is enabled by default but it often isn’t. (And, no, we have no idea why not.) Luckily, enabling it is dead easy and doing so is entirely wise.
Click the Firewall tab in the System Preferences > Security & Privacy pane we just opened. Click the padlock icon at the bottom left to unlock system settings (you’ll need to type your login password when prompted), and then click the Turn On Firewall button.
Then click the Firewall Options button and, in the dialog box that appears, click the Enable Stealth Mode box. This last step means your computer will be largely invisible on public networks, such as shared Wi-Fi in a cafe.
In the Firewall tab, click Firewall Options to make changes. Here, you’ll see a list of apps and services which are able to receive inbound connections. To add one to the list, if, say you try to run an app and it displays an error telling you it has been prevented from accepting an inbound connection, click the ‘+’ beneath the list.
It’s important to note that macOS’s Firewall, while useful, offers only limited protection from malware. That’s because it shields you from inbound traffic only. Its job is to limit which apps and services can accept incoming connections. It doesn’t provide any control over outbound connections i.e. apps and services which initiate connections. So, for example, if you download a piece of malware, OS X’s Firewall won’t stop it connecting to the internet.
Some people choose to block outgoing network connections too, so that certain apps can’t “phone home” without their knowledge. This also means accidentally installed malware is unable to leak your data without you being made aware.
Mac security tips: Passwords
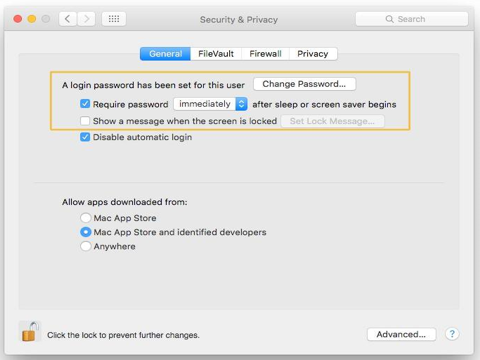
Let’s go back to the first tab in the Security & Privacy pane: the General section.
There are three settings here you should pay attention to. The first is the one which allows you to set a password for your account if you haven’t already done so. You should have a password. The next allows you to specify if a password is needed to unlock your Mac when it goes to sleep or a screen saver begins.
If you work in an office with other people, you should consider switching this setting on. You can specify how soon after sleep or the start of a screen saver the password is required. The most secure setting is ‘immediately’ but, like everything else to do with security, you need to balance security and convenience. So choose a time period that makes sense to you.
While we’re on the subject of passwords, we’ll remind you that good passwords should be difficult to remember. They should also not be written down. That, of course, presents a problem, particularly if you don’t want Safari to auto-complete them.
The solution is a password manager like 1Password or Dashlane. These apps allow you to create and store robust passwords and sync them across all your devices. Crucially, however, they encrypt the data and allow access when you type in the master password.
Mac security tips: Automatic login

Next is the Disable automatic login setting. You should check this, particularly if you use a mobile Mac. If your Mac gets stolen, you don’t want the thief to be able to access your data.
Mac security tips: Apps

At the bottom of the General page are three options relating to which apps can run on your Mac. The safest, but most limiting option, is to only allow apps from the App Store to run.
The least secure is to allow apps from anywhere.
The middle option is a good compromise, allowing you to run apps from the App Store and from developers known to Apple.
Mac security tips: FileVault
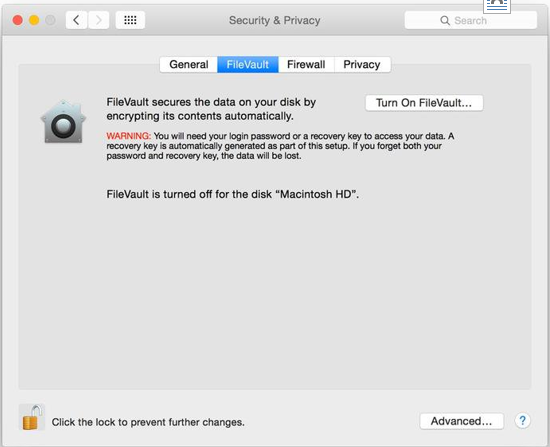
The FileVault tab allows you to encrypt all the files in your user account. To decrypt them, you’ll need to type in either your account password or the recovery key created when you switch File Vault on.
For most users, the inconvenience of having to type in a password to open a file, together with the tine it takes initially to encrypt all the files on your Mac, outweighs the security advantages. But if you have reason to keep data as secure as it can be, switch it on.
Mac security tips: Privacy
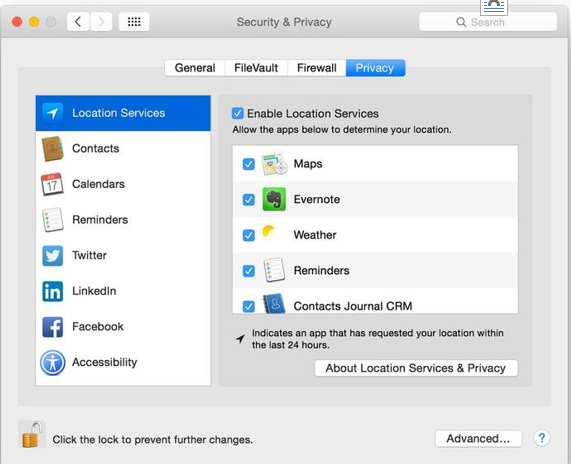
The last tab, Privacy covers a number of different controls and settings. These are listed in the window on the left of the pane. Location Services allows you to control which apps have access to your location data. You can switch Location Services off completely here, or prevent individual apps from accessing data.
Likewise, Contacts, Calendar, and Reminders allow you to specify which apps on your Mac can access the information stored in those core OS X apps. If you’ve added your Twitter, Facebook, and LinkedIn details to the Internet Accounts System Preferences pane, you can control which apps have access to those accounts here.
Lastly, but perhaps most importantly, is the Accessibility section. Despite sharing a name, this, confusingly, has nothing to do with the settings available in the Accessibility pane in the main System Preferences window. Here, you can control which apps are able to control your Mac in some way. For example, Deeper and Onyx allow you change settings which would normally require Terminal commands. To use them, you’ll need to enable them here.
Mac security tips: Safari privacy settings

Away from System Preferences, Safari has several settings that allow you to control privacy. The first is New Private Window, from the File menu, which allows you to visit websites, without a record of where you go being stored in the History menu, or anywhere else on your Mac.
The second is Clear History and Website data, in the Safari menu, which if you click it periodically, erases cached data from the sites you visit and removes them from the History menu. In Safari’s Preferences, the Privacy section allows you to prevent websites tracking you, control which sites can store cookies on your Mac, and specify how your location data is made available.
And if you’re concerned about storing website username and passwords, or personal data, go to the Auto Fill and Passwords sections and uncheck the boxes that enable those services.
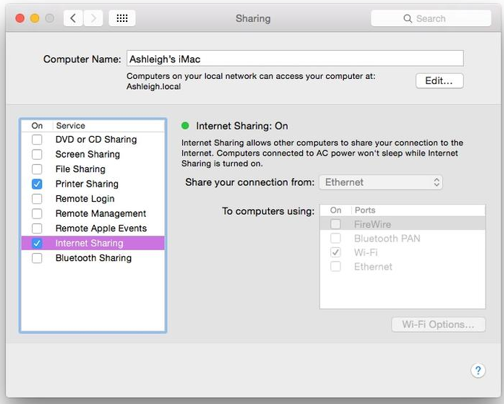
Mac security tips: Check what you’re sharing

Your Mac is able to share files with other Macs, and can share data in various other ways too – including sharing the whole screen to facilitate remote working. Once a sharing service is enabled it’s like fitting a new door or window to your house
Yes, that door or window might be considered secure – people will need a password to utilize screen sharing, for example – but there might be a flaw in the door or window that makes it not quite as impenetrable as you might think. In simple terms, it’s a good idea to turn off any sharing service you’re not using, and the majority of Macs used in the home environment should have all sharing services turned off.
To do so, open System Preferences and click the Sharing icon. Look at the list on the left, and look closely for any checks in the boxes beneath the on heading. Remove any checks you see but if in doubt take a look at the following list to make absolutely sure you’re OK disabling that particular sharing service.
Mac security tips: Screen sharing & file sharing

Screen sharing: Used mostly in corporate environments to let tech support workers see or control your screen, and perhaps perform repairs/updates. Windows and Linux computers can also use it to control your Mac’s screen via VNC. Not heard of VNC, not in a corporate environment, and never access your Mac remotely? Ensure it’s turned off.
File sharing: Lets other computers on the network access your computer’s file system, including Linux and Windows computers – technically speaking, it enables Windows File Sharing (SMB), Apple Filing Protocol (AFP), and Network File Service (NFS). Notably, the file sharing system is also used by the Back To My Mac service, which is part of iCloud and allows you to access your Mac’s files from another Mac via the internet (although it has absolutely nothing to do with iCloud Drive, which performs a similar function). If you’re not sharing files across the network, and not using Back To My Mac, then this option should be switched off.
Mac security tips: Printer sharing, remote login and more
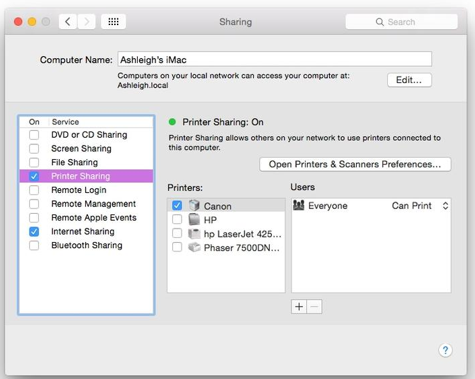
Printer sharing: Shares any printer connected to your Mac with other computers on the network, again including PCs. Should be turned off if you’re not sharing your printer, or if you don’t even have a printer attached to your Mac.
Remote login: Allows connection to your Mac via SSH/SFTP, and mostly used by techies to work at the command-line when away from their Macs. Should be turned off if that description doesn’t apply to you – and we’re pretty sure it won’t!
Remove management: Used in the corporate environment to let administrator’s access your Mac to do things like perform upgrades, or make fixes. Should be turned off in all other circumstances.
Mac security tips: Remote events, internet sharing and Bluetooth sharing
Remote Apple Events: One of Apple’s many Good Ideas From Long Ago, this lets one Mac control another to print, or do just about anything, in fact, thanks to tie-ins with AppleScript, at one point a cool joke among Mac fans was to use Remote Apple Events to make another Mac speak, via speech synthesis.
The user of that Mac would be scared half to death when his computer seemingly came to life. However, if you need Remote Apple Events in our modern age then you’ll already know all about it. The rest of us can switch it off without worry.
Internet sharing: Lets one Mac share a Net connection with other Macs. This was created in the days of dial-up internet. It’s extremely unlikely to be used now that broadband, Wi-Fi routers and home networking are the norm, so should be switched off.
Bluetooth sharing: Lets a Mac send and receive files to and from another Bluetooth-enabled device, such as a mobile phone. IPhones and iPads can’t share files this way, so you’re only likely to use it if you’ve got an Android phone. You’ll find guides online telling you how to do this. However, in all other situations this option should be turned off.
Mac security tips: Apply a firmware password
Mac OS X/macOS turns on FileVault encryption by default nowadays, which means the entire boot disk is encrypted and impossible to access unless it’s unlocked at login via the user’s password. However, that doesn’t stop somebody using a USB memory stick to boot the Mac and potentially wipe all the data from the hard disk, or simply reinstall OS X/macOS.
The solution is to apply a firmware password. Unlike with a PC’s so-called BIOS password, the Mac’s firmware password prompt will only appear if anybody tries to boot your Mac in a non-standard way, which is to say, via a USB stick, or if they try and boot to the Recovery Console. Most of the time you won’t see the password prompt.
In fact, it’s from the Recovery Console that you’ll need to activate the firmware password, so restart the computer and, just before the Apple logo appears, press and hold down Cmd+R. When the boot-time progress bar appears you can lift your fingers from the keyboard.
Select your language and location when prompted, then click the Utilities > Firmware Password Utility menu item. Follow the instructions. Be extremely careful here! If you forget the firmware password then only Apple can unlock your computer. This is probably why this feature is optional!
Mac security tips: Enable guest user
If you know anything about computer security you might be wondering if we’ve gone mad: we’re asking you to enable the guest user? Doesn’t that let anybody who’s stolen your Mac actually use it?
Well, it’s more that we’re asking you not to turn it off, because it’s a vital tool within the Find my Mac service, which is a part of iCloud that lets you attempt to track down a lost or stolen Mac. Apple says the following: “The guest account works with the Find My Mac feature of iCloud, which can help you find your Mac if you lose it. You can locate your Mac if someone finds it, logs in as a guest, then uses Safari to access the internet.”
So, don’t turn off the Guest account if you have Find my Mac enabled in iCloud. To check, open System Preferences, click the iCloud icon, and then ensure there’s a tick alongside Find My Mac at the bottom of the list at the right.
Mac security tips: Disable the FileVault ‘Security Hole’
Those who take computer security very seriously indeed point out that, when your Mac enters sleep mode (if you close the lid of a MacBook Pro, for example), there’s a potential security hole in the fact that the password required to decrypt FileVault is stored in memory.
In theory somebody could wake the computer and somehow – and we genuinely don’t know how – retrieve this key, and thereby have access to the entire disk’s contents without the need for a login password.
The only people out there likely to take advantage of this are government agencies that employ extraordinarily clever people and have unlimited budgets. It’s certainly too difficult for a burglar who steals your Mac to exploit, or a nosey colleague.
However, if you’re truly security paranoid then here’s how to stop the FileVault key being stored in memory. The only actual difference this will make in everyday use of the Mac is that sometimes you’ll be prompted to type your login password twice when waking your Mac, and your Mac will be a little slower when waking from sleep mode.
We need to do two things. First we need to switch the Mac to enter standby mode, rather than sleep mode, whenever you do something like close the lid of a MacBook Pro. In Standby mode the contents of memory are saved to disk and the computer put into a deep sleep mode that uses only a trickle of power.
Secondly, we need to tell the computer to not hold the FileVault key in memory while in Standby mode.
Both these two steps can be achieved by opening a Terminal window (you’ll find it in Utilities folder of the Applications listing in Finder) and then pasting in the following:
sudo pmset -a destroyfvkeyonstandby 1 hibernatemode 25
To turn off this feature, and renable the security “hole”, again open Terminal and type the following:
sudo pmset -a destroyfvkeyonstandby 0 hibernatemode 3
Then reboot.
Mac security tips: Check for persistent apps
Some apps on your Mac are designed to start invisibly each time you boot, and remain invisible while you’re using the computer. These are called persistent apps, and examples include the update checker apps that Google and Microsoft install to ensure Google Chrome and Microsoft Office are always up to date. Adobe installs a handful of persistent apps too as part of the Creative Cloud package.
However, malware also uses persistent apps to do their nastiness without you noticing and, to make matters worse, there are many locations in the file system where malware can hide in order to have itself started at each boot-up. We could advise you to keep an eye on each and every location, but it’s a mammoth task.
Luckily, there are two free apps that’ll do a lot of the hard work for you. KnockKnock scans these locations and will tell you what’s there. It’s not a malware scanner, so won’t tell you if what you find is dangerous or not.
That’s between you and a search engine, although a helping of common sense will do no harm – for example, the aforementioned apps for Microsoft, Google and Adobe apps are easy to spot (although as a caveat we suppose we ought to point out that it’s possible some malware might masquerade as an app from one of these companies).
The second app is from the same clever people who make KnockKnock, and it’s called BlockBlock. This runs in the background of your Mac via a menu bar icon and monitors all the locations in which persistent apps install themselves.
If any app attempts to install persistently then a pop-up dialog box will appear telling you, and it’s down to you whether you allow it or ban it. Again, BlockBlock is not an anti-malware tool so doesn’t know what’s legitimate or not. That’s for you to work out. But as forms of malware protection both KnockKnock and BlockBlock are pretty darned effective.
Mac security tips: Scan for malware
Although it’s true there’s more malware targeting Macs these days, we’re still nowhere near the tidal wave that Windows users face on a daily basis. This is also true of the malware attack that crippled the NHS – it targets only Windows PCs.
Because of this, and because OS X/macOS already features a powerful, always running yet invisible anti-malware tool called Xprotect, we reckon that antimalware software is still not a standard requirement for a Mac.
However, for peace of mind you can occasionally fire up an app like Bitdefender Virus Scanner, which simply scans through your files in order to uncover malware.
Unlike Windows antimalware apps, it doesn’t install any system monitoring software that can slow the computer down. The best news is that Bitdefender Virus Scanner is free and very easy to use. Be aware that it also finds and reports Windows malware, though.
For example, scanning my system typically shows a handful of spam mail messages containing attachments into which Windows malware has been hidden. This can be alarming but is actually harmless and, generally speaking, Windows malware can be identified because the name of it usually begins with “Win32” or “Win64”. Even though this is harmless to Mac users, Bitdefender Virus Scanner will still remove it.
In addition to Bitdeferender Virus Scanner, we also recommend the occasional use of Malwarebytes Antimalware, which focusses mostly on uncovering and removing adware – which is to say, hidden code within certain apps that aims to hijack your computing experience to show adverts on the desktop or in your web browser. Again, you can run Malwarebytes Antimalware infrequently to scan your system.
Mac security tips: Enable two-step everywhere
Two-step authentication is a system whereby your login to services or websites requires more than just your username and password. It requires an additional numeric code. This is either sent to you as something like a text message or it’s generated by a special app that runs on your mobile phone (there are many such apps but for the iPhone we recommend Authy).
We’ve already discussed how to setup two-step verification for your Apple ID (look for the Securing Your Apple ID section), and we very, very strongly recommend you set it up because it presents an insurmountable brick wall to hackers trying to gain access to your account. In fact, stop reading this now and go and do it if you haven’t already. We’ll wait here until you’ve finished.
Done it? Terrific. But now you should go off and enable two-step it for all the other sites and services you access. For example, if you use any Google services like Gmail then you can also enable two-step verification. You can enable it for Microsoft services and sites too, and for Dropbox.
Not all sites or services offer two-step verification just yet – notable hold-outs for UK users are Amazon and eBay – but a surprising number are on-board. Sites like https://twofactorauth.org provide a continually-updated list of those that do, although they tend to be biased towards American use.
Setting-up two-step verification is pretty easy. Some sites and services text you a number when you’re logging in, that you then enter when prompted, so to set them up all you need do is provide your mobile number.
For those services or sites that use an authenticator app, like the aforementioned Authy, you’ll need to switch to the app on your mobile or tablet, then choose to add a code and simply point the device’s camera at a barcode that the site displays when you opt for two-factor setup. It’s pretty straightforward.
If your device doesn’t have a camera then you can type the auth code in manually, and usually it appears just below the barcode.
Subsequently logging in to the service once two-step verification is setup will involve opening the app and typing when prompted the code displayed (usually after you’ve entered your password), or waiting for the text message/voice call to arrive and typing it when prompted.
Mac security tips: Encrypt web page look-ups
The ages-old Domain Name System, or DNS, converts the addresses we humans can read and remember – such as www.macworld.co.uk – into the numeric internet addresses that computers better understand, such as 104.16.71.73.
All computers connected to the Internet consult DNS servers. They’re provided by the Internet Service Provider as part of the overall package. The problem is that, like many things online, DNS is in no way secure.
It was invented in a different era, back when people just didn’t think about things like that. In other words, any and all requests you make for websites via DNS can be snooped upon by others while the data is in transit.
The DNSCrypt app and project overcomes this by simply encrypting DNS requests both to and from the DNS server. You can download the app from the project’s home page and setup is pretty simple once it’s installed – just open System Preferences, click theDNSCrypt icon at the bottom, then select the General tab and put checks alongside Enable DNSCrypt and Automatically Disable if Blocked. See our screenshot for an example.
You won’t notice any difference to everyday internet tasks such as web browsing when DNSCrypt is in use, although it adds a menu bar icon so you don’t forget it’s running (right-clicking this and selecting the hide option gets rid of this until you next reboot). However, with DNSCrypt running your web page look-ups are immediately more secure.
Mac security tips: Use a VPN
Never assume your Mac is safe when using a shared network, whether that’s out and about in a café, or even in location such as an office. Unfortunately, it’s extremely easy for malicious interests to spy on data you send to and from websites.
While out and about many people chose to utilise a virtual private network (VPN) service. This encrypts all data and routes it to an end point operated by the folks who run the VPN service.
Tasks such as browsing and downloading are entirely unaffected as far as the user is concerned, but anybody on the same physical network – such as another computer on the café’s shared Wi-Fi service – is blocked entirely from snooping on your Mac’s data.
Because a VPN service encrypts your data, you can also it at home to overcome internet censorship imposed by the British government and ISPs.
A variety of companies offer VPN services and they’re usually paid for via monthly subscription fees of around $5-$10. Just search Google and you’ll find many examples. However, there’s been an increasing trend recently for some companies to offer lifetime subscriptions to their VPN services for a one-off fee of around $40. For the more casual user such deals are ideal.
For impartial and expert advice, try out article Best VPNs for Mac.
Typically, VPN services come with an app that you run when you want to make use of the VPN connection, although OS X/macOS comes with a built-in VPN tool that you can use instead – just open System Preferences, click the Network icon, then click the plus button at the bottom left beneath the list of connections.
In the dialogue box that appears, click VPN from the dropdown list alongside Interface, then select the service type from the list beneath (usually it’s L2TP). Then click the Create button, and fill in the server/login details provided by the VPN service.
Mac security tips: HTTPS everywhere
For historical reasons most data is transmitted on the web in plain form and this means anybody can eavesdrop at any stage of transit. The exception is secure connections such as those made to banks, webmail services and online shopping sites. These use secure HTTP, and you can tell because the website address starts with https://.
Wouldn’t it make sense if every site used HTTPS? Making a website secure in this way is a bit more complicated and expensive than running a basic site but nonetheless there is a slow revolution happening and many sites are making the switch.
You could try adding an S to the middle of each web address – so that http://example.com becomes https://example.com. There’s an https:// version of the Google home page, for example. However, an easier way if you’re using a browser that isn’t Safari – such as Chrome or Firefox – is to install the HTTPS Everywhere browser extension. This simply (and invisibly) consults a database of sites that have an optional https:// entrance and switches you automatically should you try to access one.
Alas, because of the way it works, a true HTTPS Everywhere extension for Safari is presently impossible to implement in a way that provides maximum security. Nonetheless, the SSL Everywhere extension brings something very similar to Apple’s browser.
The only difference is that the initial data transmission when you access a site isn’t encrypted, which can provide interested hackers or snoops with a little more information than is ideal. However, once you’ve been switched over to secure HTTP – which essentially happens immediately from the user’s perspective – then everything is, of course, encrypted.
